Need good Hacking software for gaining access to restricted files? Here is a list of top 10 Hacking software.
Windows Command Prompt Cheatsheet-Command line interface (as opposed to a GUI - graphical user interface)-Used to execute programs-Commands are small programs that do something useful-There are many commands already included with Windows, but we will use a few.-A filepath is where you are in the filesystem. C: is the C drive. John the Riper- Useful Hacking Software. This useful hacking software is primarily used for cracking passwords open. Available for many flavors of Unix, DOS, Win32, BeOS and Open VMS. Supports Kerberos AFS and Windows NT/2000/XP/2003 LM Hashes. Has its own highly optimized modules for different hash types and professor architectures.
View Homework Help - 21 Command Prompt Tricks and Hacks (1).pdf from CIS IT=520-Q14 at Southern New Hampshire University. 21 Command Prompt Tricks.
Related:
There are Hacking Software for Laptop, Hacking Software for Windows 7, Hacking Software for Windows 8, Hacking software download, free PC to Mobile, Hacking software download, free for Windows XP, Hacking software free for Mobile and Free Hacking Software for PC.
1. Nmap- Simple Hacking Software
Download this simple software to uncover bugs on your PC and fix them
- Easy user interface and widely used
- Provides for port scanning and fingerprint detection
- Also provided for OS detection, scanning an IP range and alive hosts
- Rich command mode for advanced users which can combine several commands together
- Hosts its Google opensource project every year.
- Completely free with no additional costs for upgrade.
2. SuperScan- Free Hacking Software
Download this basic software for a cool scanning experience
Cached
- Superior scanning speed
- Unlimited support for IP ranges
- Improved host detection using diverse ICMP methods
- TCP SYN scanning incorporated
- Two methods of UDP Scanning’
- IP address import supporting ranges and CIDR formats
- Simple HTML report generation
- Source port scanning’
- Fast Hostname resolving
- Extensive banner grabbing
3. Cain and Abel- Password Hacking Software
This software doubles up as a password recovery tool for Microsoft Operating Systems
- WEP Cracking
- Speeds up packet capture speed through wireless packet injection
- Records VOIP conversations
- Decodes scrambled passwords
- Reveals password boxes
- Uncovers cached passwords
- Dumps protected storage passwords
4. John the Riper- Useful Hacking Software
This useful hacking software is primarily used for cracking passwords open.
- Available for many flavors of Unix, DOS, Win32, BeOS and Open VMS
- Supports Kerberos AFS and Windows NT/2000/XP/2003 LM Hashes
- Has its own highly optimized modules for different hash types and professor architectures
- Additional assembly language routines for several professor architectures, most importantly for x86-64 and x86 with SSE2
- When running on Linux distributions with glibc 2.7+, John additionally supports SHA-crypt hashes, with optional OpenMP parallelization
- Running on recent versions of Solaris, John supports and auto detects SHA-crypt and SunMD5 hashes, also with optional OpenMP parallelization.
5. FS Crack- An advanced hacking software
This advanced software serves as a front for John the Riper.
- Provides a Graphical User Interface for access to most of John’s functions
- Increases the functionality of John the Riper
- Provides detailed reports of password cracks
- Makes use of the SAM file of windows to by-pass password restrictions.
- Completely free and 100% safe and virus free.
6. Nessus Security Scanner- Hack-facilitating software
This is a network administration software which comes in a free trial version following the expiry of which it needs to be purchased.
- Features active scanners, high speed discovery, configuration auditing asset profiling, sensitive data discovery and vulnerability assessment of your security
- The scanners can be disseminated throughout an entire enterprise inside DMZs and across physically separate networks
- Functions in any environment- cloud, hybrid or on-premises
- Supports multiple technologies, more than any other vendor
- Scale of operations vary from the smallest to the largest organizations
- Comes in 4 versions- Nessus home which is free, Nessus Proffessional which needs to be purchased, Nessus Manager which has a free trial and Nessus Cloud which again needs to be purchased.
7. Wireshark-Network Protocol Analyzer
This software is a GTK+ based network protocol analyzer or sniffer that lets you capture and interactively browse the contents of network frames.
- Deep inspection of multiple protocols
- Live capture and offline examination
- Default three pane browser packet
- Runs on multiple platforms including Linux, OS X, Solaris and others
- Powerful display filters
- Exquisite VoIP analysis
- Reads and writes on many different capture file formats
- Coloring rules applicable to the packet list for quick analysis
- Output exported to XML, Postscript, CSV or plain text.
8. Live Bulk Mailer- Bulk Email application
This software is a professional high-performance bulk email software.
- Defaces spam filter of Gmail, Yahoo and Hotmail.
- Offers your proxy servers to hide your IP addresses
- Completely free of cost and no extra cost for upgradation
- Manages opt-in mailing lists for your subscribers
- Creates highly personalized HTML newsletters and messages to transfer them in quick time.
- Consists of an email tracking function
9. Website Digger-Secure Hacking Software
This software searches Google’s cache to search for vulnerabilities, anomalies, configuration issues, proprietary information and unique security snippets.
- Improved user interface in comparison to other hacking softwares
- Does not require Google API License Key
- Compatible with Proxy and TOR
- Analysis of results in real time.
- Result set which can be easily configured
- Signatures are updated.
- Unique ability to save signature selection and result set.
Cmd Commands Windows 10 Hacking
10. Putty- Free Telnet Client for Windows
This software is a free implementation of Telnet and SSH FOR Win32 and Unix platforms.
- Supports multiple variations on the secure remote terminal
- Provides user control over SSH encryption key and protocol version
- Authenticates alternate ciphers such as 3DES, Arcfour, Blowfish and DES.
- Emulates control sequences from xterm AND VT102
- Allows Local, remote or dynamic port forwarding with SSH
Thus, with our completely safe and secure hacking softwares, you can now have a crash course in the art of hacking right from the precincts of your home!
Related Posts
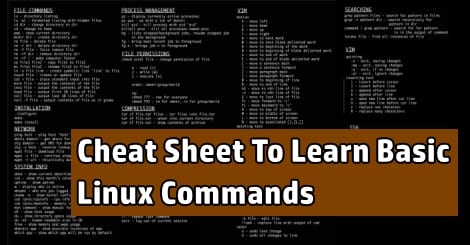
Struggling with Windows CMD hacks & command prompt tricks?
Take Command is an interactive GUI and command line environment designed for developers, administrators, and advanced users to make the Windows command prompt easy to use and far more powerful. Take Command allows you to display Windows console applications in tabbed windows, with an optional Explorer interface available for those times when you need a visual look at your folders and files. Windows batch scripting is much easier, more efficient, and vastly more powerful with the batch IDE and debugger. Take Command is a superset of the familiar CMD commands and syntax, so you're immediately more productive. (And your old command prompt tricks will still work while you learn Take Command's superior ones!)
Take Command includes hundreds of major enhancements to standard CMD commands such as COPY, DEL, DIR, and START, and adds 255 internal commands (with dialogs for most commands to simplify selecting options), more than 750 internal functions and variables, and thousands of other features.
Comments are closed.